Php Generate 256 Bit Key
Generates a random key, a-Z 0-9 with no max length
Usage
Generating an AES key. An AES key is a random bitstring of the right length. For a 128-bit AES key you need 16 bytes. For a 256-bit AES key you need 32 bytes. If you need to generate your own AES key for encrypting data, you should use a good random source. The strength of the key depends on the unpredictability of the random. Encryption Key Generator. The all-in-one ultimate online toolbox that generates all kind of keys! Every coder needs All Keys Generator in its favorites! It is provided for free and only supported by ads and donations. 64-bit 128-bit 256-bit 512-bit 1024-bit 2048-bit 4096-bit.
Use as demonstrated in the comment. This can be good to append to a url and store in a database, and check for in a site registration during email validation (i.e. http://site.com/register.php?connfirmationcode=2QwYbI0mf4exPi
Comments
The input string. If the optional rawoutput is set to TRUE, then the sha1 digest is instead returned in raw binary format with a length of 20, otherwise the returned value is a 40-character hexadecimal number. I made a PHP script that will let you sort all the available hashes on your system by generation time or by the length of the hash. It shows a general correlation on my system (longer hashes take longer to calculate) but some are faster than others, for example, sha512 makes the (joint) longest hash, but is actually only ninth slowest (from 43. I made a PHP script that will let you sort all the available hashes on your system by generation time or by the length of the hash. It shows a general correlation on my system (longer hashes take longer to calculate) but some are faster than others, for example, sha512 makes the (joint) longest hash, but is actually only ninth slowest (from 43. AES Encryption - Generating a random key in PHP duplicate. To randomly generate a secure key to to encrypt the data with. To generate a random 256-bit AES.
Tahnks !!
hi, guest your code is awesome than the original one.its user friendly and we can change our key characters easily by editing $options. i prefer your code than the original one posted.
Nice function guys. I will be using it to write a function for generating card pins for web login. Pins generated are stored on a database. When a pin is generated it is matched with the ones on the database if it exits, it is discarded if not exit, it is added to the database.
What do you think?
What about uniqueness?
fuck
nice, i use something similar
<?php
function generatekey($length)
{
$options = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
$code = ';
for($i = 0; $i < $length; $i++)
{
$key = rand(0, strlen($options) - 1);
$code .= $options[$key];
}
return $code;
}
// echo generatekey(10); // Ko9B69utve, returned result is random. not only is this good for ac validatin but has several other applicvations, eg captch ect its uses are limitless.
?>
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
256 Bit Encryption
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
Integrated Lights-Out, or iLO, is a proprietary embedded server management technology by Hewlett-Packard which provides out-of-band management facilities. Hp ilo 4 download.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
We are now happy reviewing everyone that amazing hottest tool. Simply speaking download this useful application and just test it for you. Generate key file with the keygen.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
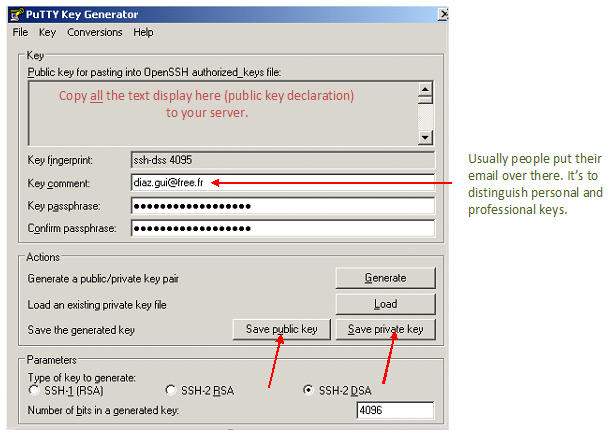
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Php Generate 256 Bit Key Generator
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.