Generate Ssh Keys In Linux
May 27, 2010 H ow do I generate ssh RSA keys under Linux operating systems? You need to use the ssh-keygen command as follows to generate RSA keys (open terminal and type the following command): ssh-keygen -t rsa OR ssh-keygen. May 05, 2019 This tutorial explains how to generate SSH keys on Windows with PuTTYgen. We will also show you how to set up an SSH key-based authentication and connect to your remote Linux servers without entering a password. To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods: Create a Linux virtual machine with the Azure portal Create a Linux virtual machine with the Azure CLI Create a Linux VM using an Azure template. Nov 10, 2011 How to Generate A Public/Private SSH Key Linux By Damien – Posted on Nov 10, 2011 Nov 18, 2011 in Linux If you are using SSH frequently to connect to a remote host, one of the way to secure the connection is to use a public/private SSH key so no password is transmitted over the network and it can prevent against brute force attack. Red Hat Enterprise Linux 6 uses SSH Protocol 2 and RSA keys by default (see Section 14.1.3, “Protocol Versions” for more information). Important Do not generate key pairs as root, as only root would be able to use those keys.
This article or section needs expansion.
SSH keys can serve as a means of identifying yourself to an SSH server using public-key cryptography and challenge-response authentication. The major advantage of key-based authentication is that in contrast to password authentication it is not prone to brute-force attacks and you do not expose valid credentials, if the server has been compromised.[1]
Furthermore SSH key authentication can be more convenient than the more traditional password authentication. When used with a program known as an SSH agent, SSH keys can allow you to connect to a server, or multiple servers, without having to remember or enter your password for each system.
Key-based authentication is not without its drawbacks and may not be appropriate for all environments, but in many circumstances it can offer some strong advantages. A general understanding of how SSH keys work will help you decide how and when to use them to meet your needs.
This article assumes you already have a basic understanding of the Secure Shell protocol and have installed the openssh package.
- 2Generating an SSH key pair
- 2.1Choosing the authentication key type
- 2.2Choosing the key location and passphrase
- 3Copying the public key to the remote server
- 4SSH agents
- 4.1ssh-agent
- 4.3Keychain
- 4.4x11-ssh-askpass
- 4.5pam_ssh
- 5Troubleshooting
Background
SSH keys are always generated in pairs with one known as the private key and the other as the public key. The private key is known only to you and it should be safely guarded. By contrast, the public key can be shared freely with any SSH server to which you wish to connect.
If an SSH server has your public key on file and sees you requesting a connection, it uses your public key to construct and send you a challenge. This challenge is an encrypted message and it must be met with the appropriate response before the server will grant you access. What makes this coded message particularly secure is that it can only be understood by the private key holder. While the public key can be used to encrypt the message, it cannot be used to decrypt that very same message. Only you, the holder of the private key, will be able to correctly understand the challenge and produce the proper response.
This challenge-response phase happens behind the scenes and is invisible to the user. As long as you hold the private key, which is typically stored in the ~/.ssh/ directory, your SSH client should be able to reply with the appropriate response to the server.
A private key is a guarded secret and as such it is advisable to store it on disk in an encrypted form. When the encrypted private key is required, a passphrase must first be entered in order to decrypt it. While this might superficially appear as though you are providing a login password to the SSH server, the passphrase is only used to decrypt the private key on the local system. The passphrase is not transmitted over the network.
Generating an SSH key pair
An SSH key pair can be generated by running the ssh-keygen command, defaulting to 3072-bit RSA (and SHA256) which the ssh-keygen(1) man page says is 'generally considered sufficient' and should be compatible with virtually all clients and servers:
The randomart image was introduced in OpenSSH 5.1 as an easier means of visually identifying the key fingerprint.
-a switch to specify the number of KDF rounds on the password encryption.You can also add an optional comment field to the public key with the -C switch, to more easily identify it in places such as ~/.ssh/known_hosts, ~/.ssh/authorized_keys and ssh-add -L output. For example:
will add a comment saying which user created the key on which machine and when.
Choosing the authentication key type
OpenSSH supports several signing algorithms (for authentication keys) which can be divided in two groups depending on the mathematical properties they exploit:
- DSA and RSA, which rely on the practical difficulty of factoring the product of two large prime numbers,
- ECDSA and Ed25519, which rely on the elliptic curve discrete logarithm problem. (example)
Elliptic curve cryptography (ECC) algorithms are a more recent addition to public key cryptosystems. One of their main advantages is their ability to provide the same level of security with smaller keys, which makes for less computationally intensive operations (i.e. faster key creation, encryption and decryption) and reduced storage and transmission requirements.
OpenSSH 7.0 deprecated and disabled support for DSA keys due to discovered vulnerabilities, therefore the choice of cryptosystem lies within RSA or one of the two types of ECC.
#RSA keys will give you the greatest portability, while #Ed25519 will give you the best security but requires recent versions of client & server[2][dead link 2020-04-02 ⓘ]. #ECDSA is likely more compatible than Ed25519 (though still less than RSA), but suspicions exist about its security (see below).
RSA
ssh-keygen defaults to RSA therefore there is no need to specify it with the -t option. It provides the best compatibility of all algorithms but requires the key size to be larger to provide sufficient security.
Minimum key size is 1024 bits, default is 3072 (see ssh-keygen(1)) and maximum is 16384.
If you wish to generate a stronger RSA key pair (e.g. to guard against cutting-edge or unknown attacks and more sophisticated attackers), simply specify the -b option with a higher bit value than the default:
Be aware though that there are diminishing returns in using longer keys.[3][4] The GnuPG FAQ reads: 'If you need more security than RSA-2048 offers, the way to go would be to switch to elliptical curve cryptography — not to continue using RSA'.[5]
On the other hand, the latest iteration of the NSA Fact Sheet Suite B Cryptography[dead link 2020-04-02 ⓘ] suggests a minimum 3072-bit modulus for RSA while '[preparing] for the upcoming quantum resistant algorithm transition'.[6]
ECDSA
The Elliptic Curve Digital Signature Algorithm (ECDSA) was introduced as the preferred algorithm for authentication in OpenSSH 5.7. Some vendors also disable the required implementations due to potential patent issues.
There are two sorts of concerns with it:
- Political concerns, the trustworthiness of NIST-produced curves being questioned after revelations that the NSA willingly inserts backdoors into softwares, hardware components and published standards were made; well-known cryptographers haveexpresseddoubts about how the NIST curves were designed, and voluntary tainting has already beenproved in the past.
- Technical concerns, about the difficulty to properly implement the standard and the slowness and design flaws which reduce security in insufficiently precautious implementations.
Battlefield 4 premium key generator no survey. Both of those concerns are best summarized in libssh curve25519 introduction. Although the political concerns are still subject to debate, there is a clear consensus that #Ed25519 is technically superior and should therefore be preferred.
Ed25519
Ed25519 was introduced in OpenSSH 6.5 of January 2014: 'Ed25519 is an elliptic curve signature scheme that offers better security than ECDSA and DSA and good performance'. Its main strengths are its speed, its constant-time run time (and resistance against side-channel attacks), and its lack of nebulous hard-coded constants.[7] See also this blog post by a Mozilla developer on how it works.
It is already implemented in many applications and libraries and is the default key exchange algorithm (which is different from key signature) in OpenSSH.
Ed25519 key pairs can be generated with:
There is no need to set the key size, as all Ed25519 keys are 256 bits.
Keep in mind that older SSH clients and servers may not support these keys.
Choosing the key location and passphrase
Upon issuing the ssh-keygen command, you will be prompted for the desired name and location of your private key. By default, keys are stored in the ~/.ssh/ directory and named according to the type of encryption used. You are advised to accept the default name and location in order for later code examples in this article to work properly.
When prompted for a passphrase, choose something that will be hard to guess if you have the security of your private key in mind. A longer, more random password will generally be stronger and harder to crack should it fall into the wrong hands.
It is also possible to create your private key without a passphrase. While this can be convenient, you need to be aware of the associated risks. Without a passphrase, your private key will be stored on disk in an unencrypted form. Anyone who gains access to your private key file will then be able to assume your identity on any SSH server to which you connect using key-based authentication. Furthermore, without a passphrase, you must also trust the root user, as he can bypass file permissions and will be able to access your unencrypted private key file at any time.
Changing the private key's passphrase without changing the key
If the originally chosen SSH key passphrase is undesirable or must be changed, one can use the ssh-keygen command to change the passphrase without changing the actual key. This can also be used to change the password encoding format to the new standard.
Managing multiple keys
It is possible — although controversial [8][9] — to use the same SSH key pair for multiple hosts.
On the other hand, it is rather easy to maintain distinct keys for multiple hosts by using the IdentityFile directive in your openSSH config file:
See ssh_config(5) for full description of these options.
Storing SSH keys on hardware tokens
SSH keys can also be stored on a security token like a smart card or a USB token. This has the advantage that the private key is stored securely on the token instead of being stored on disk. When using a security token the sensitive private key is also never present in the RAM of the PC; the cryptographic operations are performed on the token itself. A cryptographic token has the additional advantage that it is not bound to a single computer; it can easily be removed from the computer and carried around to be used on other computers.
Examples are hardware tokens are described in:
- Yubikey#OpenSSH Native OpenSSH support for FIDO/U2F keys
Copying the public key to the remote server
This article or section needs expansion.
Once you have generated a key pair, you will need to copy the public key to the remote server so that it will use SSH key authentication. The public key file shares the same name as the private key except that it is appended with a .pub extension. Note that the private key is not shared and remains on the local machine.
Simple method
sh shell such as tcsh as default and uses OpenSSH older than 6.6.1p1. See this bug report.Generate Ssh Keys In Linux
If your key file is ~/.ssh/id_rsa.pub you can simply enter the following command.
If your username differs on remote machine, be sure to prepend the username followed by @ to the server name.
If your public key filename is anything other than the default of ~/.ssh/id_rsa.pub you will get an error stating /usr/bin/ssh-copy-id: ERROR: No identities found. In this case, you must explicitly provide the location of the public key.
If the ssh server is listening on a port other than default of 22, be sure to include it within the host argument.
Manual method
By default, for OpenSSH, the public key needs to be concatenated with ~/.ssh/authorized_keys. Begin by copying the public key to the remote server.
The above example copies the public key (id_ecdsa.pub) to your home directory on the remote server via scp. Do not forget to include the : at the end of the server address. Also note that the name of your public key may differ from the example given.
On the remote server, you will need to create the ~/.ssh directory if it does not yet exist and append your public key to the authorized_keys file.
The last two commands remove the public key file from the server and set the permissions on the authorized_keys file such that it is only readable and writable by you, the owner.
SSH agents

If your private key is encrypted with a passphrase, this passphrase must be entered every time you attempt to connect to an SSH server using public-key authentication. Each individual invocation of ssh or scp will need the passphrase in order to decrypt your private key before authentication can proceed.
An SSH agent is a program which caches your decrypted private keys and provides them to SSH client programs on your behalf. In this arrangement, you must only provide your passphrase once, when adding your private key to the agent's cache. This facility can be of great convenience when making frequent SSH connections.
An agent is typically configured to run automatically upon login and persist for the duration of your login session. A variety of agents, front-ends, and configurations exist to achieve this effect. This section provides an overview of a number of different solutions which can be adapted to meet your specific needs.
ssh-agent
ssh-agent is the default agent included with OpenSSH. It can be used directly or serve as the back-end to a few of the front-end solutions mentioned later in this section. When ssh-agent is run, it forks to background and prints necessary environment variables. E.g.
To make use of these variables, run the command through the eval command.
Once ssh-agent is running, you will need to add your private key to its cache:
If your private key is encrypted, ssh-add will prompt you to enter your passphrase. Once your private key has been successfully added to the agent you will be able to make SSH connections without having to enter your passphrase.
ssh clients, including git store keys in the agent on first use, add the configuration setting AddKeysToAgent yes to ~/.ssh/config. Other possible values are confirm, ask and no (default).In order to start the agent automatically and make sure that only one ssh-agent process runs at a time, add the following to your ~/.bashrc:
This will run a ssh-agent process if there is not one already, and save the output thereof. If there is one running already, we retrieve the cached ssh-agent output and evaluate it which will set the necessary environment variables.
There also exist a number of front-ends to ssh-agent and alternative agents described later in this section which avoid this problem.
Start ssh-agent with systemd user
It is possible to use the systemd/User facilities to start the agent. Use this if you would like your ssh agent to run when you are logged in, regardless of whether x is running.
Add SSH_AUTH_SOCK DEFAULT='${XDG_RUNTIME_DIR}/ssh-agent.socket' to ~/.pam_environment. Then enable or start the service with the --user flag.
ssh-agent as a wrapper program
An alternative way to start ssh-agent (with, say, each X session) is described in this ssh-agent tutorial by UC Berkeley Labs. A basic use case is if you normally begin X with the startx command, you can instead prefix it with ssh-agent like so:
And so you do not even need to think about it you can put an alias in your .bash_aliases file or equivalent:
Doing it this way avoids the problem of having extraneous ssh-agent instances floating around between login sessions. Exactly one instance will live and die with the entire X session.
ssh-agent startx, you can add eval $(ssh-agent) to ~/.xinitrc.See the below notes on using x11-ssh-askpass with ssh-add for an idea on how to immediately add your key to the agent.
GnuPG Agent
Generate Ssh Key Linux Mint
The gpg-agent has OpenSSH agent emulation. See GnuPG#SSH agent for necessary configuration.
Keychain
Keychain is a program designed to help you easily manage your SSH keys with minimal user interaction. It is implemented as a shell script which drives both ssh-agent and ssh-add. A notable feature of Keychain is that it can maintain a single ssh-agent process across multiple login sessions. This means that you only need to enter your passphrase once each time your local machine is booted.
Installation
Install the keychain package.
Configuration
-Q, --quick option has the unexpected side-effect of making keychain switch to a newly-spawned ssh-agent upon relogin (at least on systems using GNOME), forcing you to re-add all the previously registered keys.Add a line similar to the following to your shell configuration file, e.g. if using Bash:
~/.bashrc is used instead of the upstream suggested ~/.bash_profile because on Arch it is sourced by both login and non-login shells, making it suitable for textual and graphical environments alike. See Bash#Invocation for more information on the difference between those.In the above example,
- the
--evalswitch outputs lines to be evaluated by the openingevalcommand; this sets the necessary environments variables for SSH client to be able to find your agent. --quietwill limit output to warnings, errors, and user prompts.
Multiple keys can be specified on the command line, as shown in the example. By default keychain will look for key pairs in the ~/.ssh/ directory, but absolute path can be used for keys in non-standard location. You may also use the --confhost option to inform keychain to look in ~/.ssh/config for IdentityFile settings defined for particular hosts, and use these paths to locate keys.
See keychain --help or keychain(1) for details on setting keychain for other shells.
To test Keychain, simply open a new terminal emulator or log out and back in your session. It should prompt you for the passphrase of the specified private key(s) (if applicable), either using the program set in $SSH_ASKPASS or on the terminal.
Because Keychain reuses the same ssh-agent process on successive logins, you should not have to enter your passphrase the next time you log in or open a new terminal. You will only be prompted for your passphrase once each time the machine is rebooted.
Tips
- keychain expects public key files to exist in the same directory as their private counterparts, with a
.pubextension. If the private key is a symlink, the public key can be found alongside the symlink or in the same directory as the symlink target (this capability requires thereadlinkcommand to be available on the system).
- to disable the graphical prompt and always enter your passphrase on the terminal, use the
--noguioption. This allows to copy-paste long passphrases from a password manager for example.
- if you do not want to be immediately prompted for unlocking the keys but rather wait until they are needed, use the
--noaskoption.
--agents option, e.g.--agents ssh,gpg. See keychain(1).x11-ssh-askpass
The x11-ssh-askpass package provides a graphical dialog for entering your passhrase when running an X session. x11-ssh-askpass depends only on the libx11 and libxt libraries, and the appearance of x11-ssh-askpass is customizable. While it can be invoked by the ssh-add program, which will then load your decrypted keys into ssh-agent, the following instructions will, instead, configure x11-ssh-askpass to be invoked by the aforementioned Keychain script.
Install the keychain and x11-ssh-askpass packages.
Edit your ~/.xinitrc file to include the following lines, replacing the name and location of your private key if necessary. Be sure to place these commands before the line which invokes your window manager.
In the above example, the first line invokes keychain and passes the name and location of your private key. If this is not the first time keychain was invoked, the following two lines load the contents of $HOSTNAME-sh and $HOSTNAME-sh-gpg, if they exist. These files store the environment variables of the previous instance of keychain.
Calling x11-ssh-askpass with ssh-add
The ssh-add manual page specifies that, in addition to needing the DISPLAY variable defined, you also need SSH_ASKPASS set to the name of your askpass program (in this case x11-ssh-askpass). It bears keeping in mind that the default Arch Linux installation places the x11-ssh-askpass binary in /usr/lib/ssh/, which will not be in most people's PATH. This is a little annoying, not only when declaring the SSH_ASKPASS variable, but also when theming. You have to specify the full path everywhere. Both inconveniences can be solved simultaneously by symlinking:
This is assuming that ~/bin is in your PATH. So now in your .xinitrc, before calling your window manager, one just needs to export the SSH_ASKPASS environment variable:
and your X resources will contain something like:
Doing it this way works well with the above method on using ssh-agent as a wrapper program. You start X with ssh-agent startx and then add ssh-add to your window manager's list of start-up programs.
Theming
The appearance of the x11-ssh-askpass dialog can be customized by setting its associated X resources. Some examples are the .ad files at https://github.com/sigmavirus24/x11-ssh-askpass. See x11-ssh-askpass(1)[dead link 2019-05-05] for full details.
Alternative passphrase dialogs
There are other passphrase dialog programs which can be used instead of x11-ssh-askpass. The following list provides some alternative solutions.
- ksshaskpass uses the KDE Wallet.
- openssh-askpass uses the Qt library.
pam_ssh
The pam_ssh project exists to provide a Pluggable Authentication Module (PAM) for SSH private keys. This module can provide single sign-on behavior for your SSH connections. On login, your SSH private key passphrase can be entered in place of, or in addition to, your traditional system password. Once you have been authenticated, the pam_ssh module spawns ssh-agent to store your decrypted private key for the duration of the session.
To enable single sign-on behavior at the tty login prompt, install the unofficial pam_sshAUR package.
~/.ssh/login-keys.d/.Create a symlink to your private key file and place it in ~/.ssh/login-keys.d/. Replace the id_rsa in the example below with the name of your own private key file.
Edit the /etc/pam.d/login configuration file to include the text highlighted in bold in the example below. The order in which these lines appear is significiant and can affect login behavior.
In the above example, login authentication initially proceeds as it normally would, with the user being prompted to enter his user password. The additional auth authentication rule added to the end of the authentication stack then instructs the pam_ssh module to try to decrypt any private keys found in the ~/.ssh/login-keys.d directory. The try_first_pass option is passed to the pam_ssh module, instructing it to first try to decrypt any SSH private keys using the previously entered user password. If the user's private key passphrase and user password are the same, this should succeed and the user will not be prompted to enter the same password twice. In the case where the user's private key passphrase user password differ, the pam_ssh module will prompt the user to enter the SSH passphrase after the user password has been entered. The optional control value ensures that users without an SSH private key are still able to log in. In this way, the use of pam_ssh will be transparent to users without an SSH private key.
If you use another means of logging in, such as an X11 display manager like SLiM or XDM and you would like it to provide similar functionality, you must edit its associated PAM configuration file in a similar fashion. Packages providing support for PAM typically place a default configuration file in the /etc/pam.d/ directory.
Further details on how to use pam_ssh and a list of its options can be found in the pam_ssh(8) man page.
Using a different password to unlock the SSH key
If you want to unlock the SSH keys or not depending on whether you use your key's passphrase or the (different!) login password, you can modify /etc/pam.d/system-auth to
For an explanation, see [10].
Known issues with pam_ssh
Work on the pam_ssh project is infrequent and the documentation provided is sparse. You should be aware of some of its limitations which are not mentioned in the package itself.
- Versions of pam_ssh prior to version 2.0 do not support SSH keys employing the newer option of ECDSA (elliptic curve) cryptography. If you are using earlier versions of pam_ssh you must use either RSA or DSA keys.
- The
ssh-agentprocess spawned by pam_ssh does not persist between user logins. If you like to keep a GNU Screen session active between logins you may notice when reattaching to your screen session that it can no longer communicate with ssh-agent. This is because the GNU Screen environment and those of its children will still reference the instance of ssh-agent which existed when GNU Screen was invoked but was subsequently killed in a previous logout. The Keychain front-end avoids this problem by keeping the ssh-agent process alive between logins.
pam_exec-ssh
As an alternative to pam_ssh you can use pam_exec-sshAUR. It is a shell script that uses pam_exec. Help for configuration can be found upstream.
GNOME Keyring
If you use the GNOME desktop, the GNOME Keyring tool can be used as an SSH agent. See the GNOME Keyring article for further details.
Store SSH keys with Kwallet
For instructions on how to use kwallet to store your SSH keys, see KDE Wallet#Using the KDE Wallet to store ssh key passphrases.
KeePass2 with KeeAgent plugin
KeeAgent is a plugin for KeePass that allows SSH keys stored in a KeePass database to be used for SSH authentication by other programs.
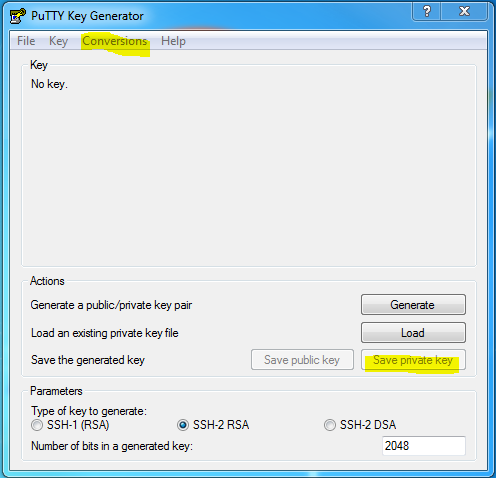
- Supports both PuTTY and OpenSSH private key formats.
- Works with native SSH agent on Linux/Mac and with PuTTY on Windows.
See KeePass#Plugin Installation in KeePass or install the keepass-plugin-keeagent package.
This agent can be used directly, by matching KeeAgent socket: KeePass -> Tools -> Options -> KeeAgent -> Agent mode socket file -> %XDG_RUNTIME_DIR%/keeagent.socket-and environment variable:export SSH_AUTH_SOCK='$XDG_RUNTIME_DIR'/keeagent.socket'.
KeePassXC
The KeePassXC fork of KeePass supports being used as an SSH agent by default. It is also compatible with KeeAgent's database format.
Troubleshooting
Key ignored by the server
- If it appears that the SSH server is ignoring your keys, ensure that you have the proper permissions set on all relevant files.
- For the local machine:
- For the remote machine:
- If that does not solve the problem you may try temporarily setting
StrictModestonoin/etc/ssh/sshd_config. If authentication withStrictModes offis successful, it is likely an issue with file permissions persists.
- Make sure keys in
~/.ssh/authorized_keysare entered correctly and only use one single line. - Make sure the remote machine supports the type of keys you are using: some servers do not support ECDSA keys, try using RSA or DSA keys instead, see #Generating an SSH key pair.
- You may want to use debug mode and monitor the output while connecting:
See also
- OpenSSH key management: Part 1, Part 2, Part 3
Create Ssh Key Pair
With a secure shell (SSH) key pair, you can create a Linux virtual machine on Azure that defaults to using SSH keys for authentication, eliminating the need for passwords to sign in. VMs created with the Azure portal, Azure CLI, Resource Manager templates, or other tools can include your SSH public key as part of the deployment, which sets up SSH key authentication for SSH connections.
This article provides detailed background and steps to create and manage an SSH RSA public-private key file pair for SSH client connections. If you want quick commands, see How to create an SSH public-private key pair for Linux VMs in Azure.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Overview of SSH and keys
SSH is an encrypted connection protocol that allows secure sign-ins over unsecured connections. SSH is the default connection protocol for Linux VMs hosted in Azure. Although SSH itself provides an encrypted connection, using passwords with SSH connections still leaves the VM vulnerable to brute-force attacks or guessing of passwords. A more secure and preferred method of connecting to a VM using SSH is by using a public-private key pair, also known as SSH keys.
The public key is placed on your Linux VM, or any other service that you wish to use with public-key cryptography.
The private key remains on your local system. Protect this private key. Do not share it.
When you use an SSH client to connect to your Linux VM (which has the public key), the remote VM tests the client to make sure it possesses the private key. If the client has the private key, it's granted access to the VM.
Depending on your organization's security policies, you can reuse a single public-private key pair to access multiple Azure VMs and services. You do not need a separate pair of keys for each VM or service you wish to access.
Generate Ssh Key Linux Git
Your public key can be shared with anyone, but only you (or your local security infrastructure) should possess your private key.
Private key passphrase
The SSH private key should have a very secure passphrase to safeguard it. This passphrase is just to access the private SSH key file and is not the user account password. When you add a passphrase to your SSH key, it encrypts the private key using 128-bit AES, so that the private key is useless without the passphrase to decrypt it. If an attacker stole your private key and that key did not have a passphrase, they would be able to use that private key to sign in to any servers that have the corresponding public key. If a private key is protected by a passphrase, it cannot be used by that attacker, providing an additional layer of security for your infrastructure on Azure.
Supported SSH key formats
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
SSH keys use and benefits
When you create an Azure VM by specifying the public key, Azure copies the public key (in the .pub format) to the ~/.ssh/authorized_keys folder on the VM. SSH keys in ~/.ssh/authorized_keys are used to challenge the client to match the corresponding private key on an SSH connection. In an Azure Linux VM that uses SSH keys for authentication, Azure configures the SSHD server to not allow password sign-in, only SSH keys. Therefore, by creating an Azure Linux VM with SSH keys, you can help secure the VM deployment and save yourself the typical post-deployment configuration step of disabling passwords in the sshd_config file.
If you do not wish to use SSH keys, you can set up your Linux VM to use password authentication. If your VM is not exposed to the Internet, using passwords may be sufficient. However, you still need to manage your passwords for each Linux VM and maintain healthy password policies and practices, such as minimum password length and regular updates. Using SSH keys reduces the complexity of managing individual credentials across multiple VMs.
Generate keys with ssh-keygen
To create the keys, a preferred command is ssh-keygen, which is available with OpenSSH utilities in the Azure Cloud Shell, a macOS or Linux host, the Windows Subsystem for Linux, and other tools. ssh-keygen asks a series of questions and then writes a private key and a matching public key.
SSH keys are by default kept in the ~/.ssh directory. If you do not have a ~/.ssh directory, the ssh-keygen command creates it for you with the correct permissions.
Basic example
The following ssh-keygen command generates 2048-bit SSH RSA public and private key files by default in the ~/.ssh directory. If an SSH key pair exists in the current location, those files are overwritten.
Detailed example
The following example shows additional command options to create an SSH RSA key pair. If an SSH key pair exists in the current location, those files are overwritten.
Command explained
ssh-keygen = the program used to create the keys
-m PEM = format the key as PEM
-t rsa = type of key to create, in this case in the RSA format
-b 4096 = the number of bits in the key, in this case 4096
-C 'azureuser@myserver' = a comment appended to the end of the public key file to easily identify it. Normally an email address is used as the comment, but use whatever works best for your infrastructure.
-f ~/.ssh/mykeys/myprivatekey = the filename of the private key file, if you choose not to use the default name. A corresponding public key file appended with .pub is generated in the same directory. The directory must exist.
-N mypassphrase = an additional passphrase used to access the private key file.
Example of ssh-keygen
Saved key files
Enter file in which to save the key (/home/azureuser/.ssh/id_rsa): ~/.ssh/id_rsa
The key pair name for this article. Having a key pair named id_rsa is the default; some tools might expect the id_rsa private key file name, so having one is a good idea. The directory ~/.ssh/ is the default location for SSH key pairs and the SSH config file. If not specified with a full path, ssh-keygen creates the keys in the current working directory, not the default ~/.ssh.
List of the ~/.ssh directory
Key passphrase
Enter passphrase (empty for no passphrase):
It is strongly recommended to add a passphrase to your private key. Without a passphrase to protect the key file, anyone with the file can use it to sign in to any server that has the corresponding public key. Adding a passphrase offers more protection in case someone is able to gain access to your private key file, giving you time to change the keys.
Generate keys automatically during deployment
If you use the Azure CLI to create your VM, you can optionally generate SSH public and private key files by running the az vm create command with the --generate-ssh-keys option. The keys are stored in the ~/.ssh directory. Note that this command option does not overwrite keys if they already exist in that location.
Provide SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, provide your SSH public key when creating the VM using the Azure portal, CLI, Resource Manager templates, or other methods. When using the portal, you enter the public key itself. If you use the Azure CLI to create your VM with an existing public key, specify the value or location of this public key by running the az vm create command with the --ssh-key-value option.
If you're not familiar with the format of an SSH public key, you can see your public key by running cat as follows, replacing ~/.ssh/id_rsa.pub with your own public key file location:
Output is similar to the following (here redacted):
If you copy and paste the contents of the public key file into the Azure portal or a Resource Manager template, make sure you don't copy any additional whitespace or introduce additional line breaks. For example, if you use macOS, you can pipe the public key file (by default, ~/.ssh/id_rsa.pub) to pbcopy to copy the contents (there are other Linux programs that do the same thing, such as xclip).
If you prefer to use a public key that is in a multiline format, you can generate an RFC4716 formatted key in a pem container from the public key you previously created.
To create a RFC4716 formatted key from an existing SSH public key:
SSH to your VM with an SSH client
With the public key deployed on your Azure VM, and the private key on your local system, SSH to your VM using the IP address or DNS name of your VM. Replace azureuser and myvm.westus.cloudapp.azure.com in the following command with the administrator user name and the fully qualified domain name (or IP address):
If you provided a passphrase when you created your key pair, enter the passphrase when prompted during the sign-in process. (The server is added to your ~/.ssh/known_hosts folder, and you won't be asked to connect again until the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.)
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Use ssh-agent to store your private key passphrase
To avoid typing your private key file passphrase with every SSH sign-in, you can use ssh-agent to cache your private key file passphrase. If you are using a Mac, the macOS Keychain securely stores the private key passphrase when you invoke ssh-agent.
Verify and use ssh-agent and ssh-add to inform the SSH system about the key files so that you do not need to use the passphrase interactively.
Now add the private key to ssh-agent using the command ssh-add.
The private key passphrase is now stored in ssh-agent.
Use ssh-copy-id to copy the key to an existing VM
If you have already created a VM, you can install the new SSH public key to your Linux VM with a command similar to the following:
Create and configure an SSH config file
You can create and configure an SSH config file (~/.ssh/config) to speed up log-ins and to optimize your SSH client behavior.
The following example shows a simple configuration that you can use to quickly sign in as a user to a specific VM using the default SSH private key.
Dawn of war 2 key code generator. May 25, 2017 Warhammer 40,000: Dawn of War II Keygen is here and it is FREE and 100% working and legit. With Warhammer 40,000: Dawn of War II Keygen you can Get a cd-key which you can activate Warhammer 40,000: Dawn of War II.
Create the file
Edit the file to add the new SSH configuration
Example configuration
Add configuration settings appropriate for your host VM.
You can add configurations for additional hosts to enable each to use its own dedicated key pair. See SSH config file for more advanced configuration options.
Now that you have an SSH key pair and a configured SSH config file, you are able to sign in to your Linux VM quickly and securely. When you run the following command, SSH locates and loads any settings from the Host myvm block in the SSH config file.
The first time you sign in to a server using an SSH key, the command prompts you for the passphrase for that key file.
Next steps
Next up is to create Azure Linux VMs using the new SSH public key. Azure VMs that are created with an SSH public key as the sign-in are better secured than VMs created with the default sign-in method, passwords.